How the Eaton Gigabit Network Card protects against supply chain cyber attacks
2:22
Eaton’s Network-M2 card for power quality connectivity provides protection from a supply chain attack. In addition to enterprise standard information security mitigations, feature branches undergo an independent code review process before being merged. M2 firmware is digitally signed, preventing the installation of unauthorized or corrupted firmware. M2 firmware is encrypted, preventing analysis for vulnerabilities. The M2 file system is digitally signed, preventing unauthorized changes to your data. Eaton’s Nework-M2 card transforms a UPS or Uninterruptable Power Supply into an enterprise level IoT device. Learn more at https://www.eaton.com/cybersecurity
Eaton’s Network-M2 card for power quality connectivity provides protection from a supply chain attack. In addition to enterprise standard information security mitigations, feature branches undergo an independent code review process before being merged. M2 firmware is digitally signed, preventing the installation of unauthorized or corrupted firmware. M2 firmware is encrypted, preventing analysis for vulnerabilities. The M2 file system is digitally signed, preventing unauthorized changes to your data. Eaton’s Nework-M2 card transforms a UPS or Uninterruptable Power Supply into an enterprise level IoT device. Learn more at https://www.eaton.com/cybersecurity
Related videos for "network card network"
-
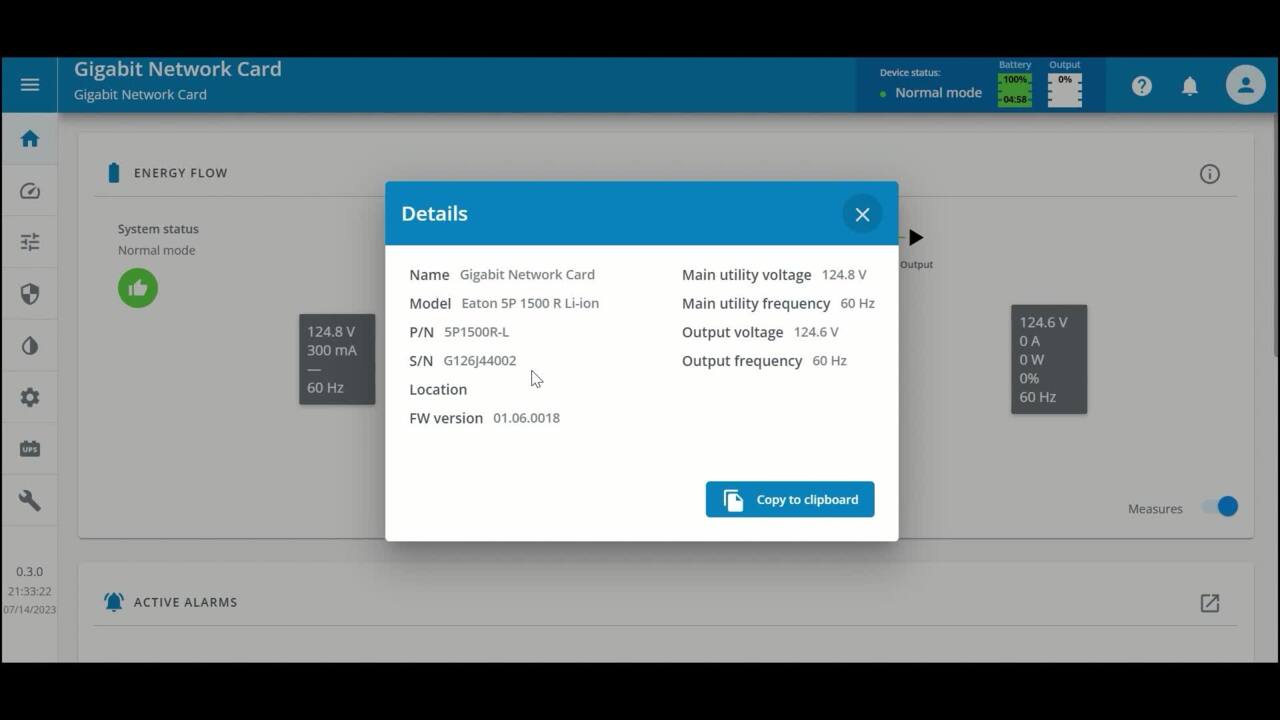
Eaton Gigabit Network Card (Network-M3): Overview
8:21
Eaton's latest network management card improves business continuity by providing warnings of pending issues to administrators and helping to perform orderly shutdown of servers and storage.
-
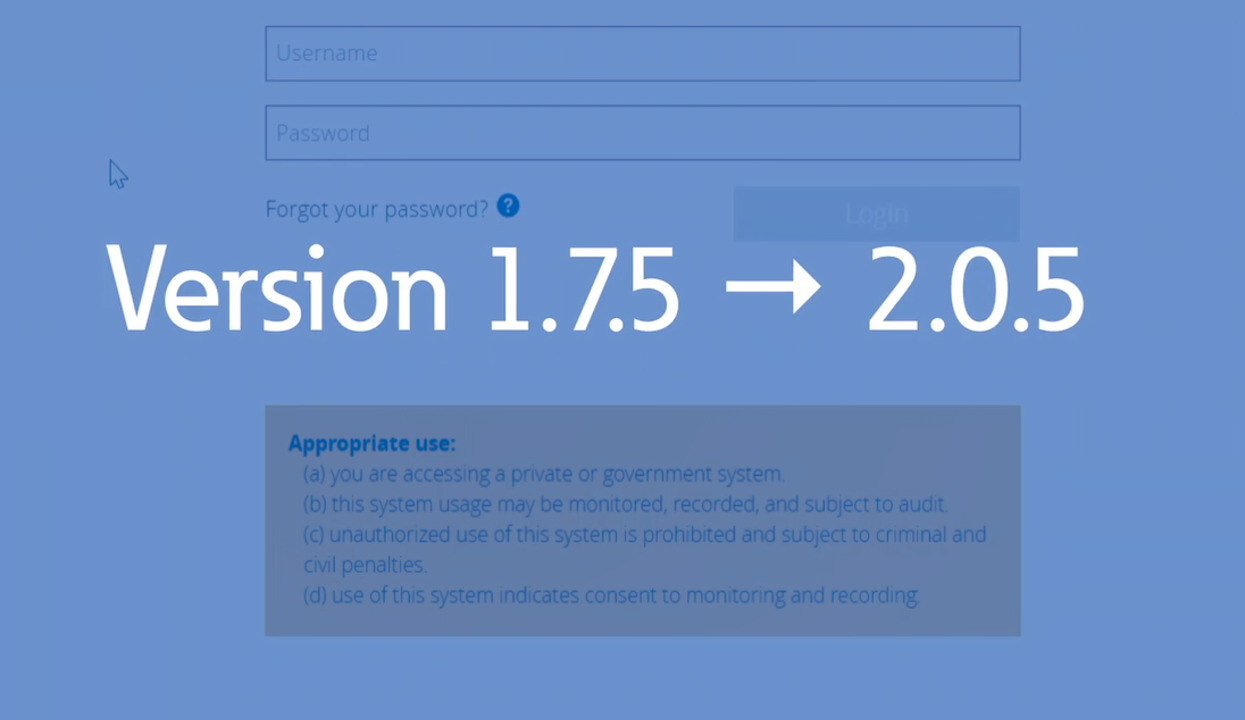
Eaton Gigabit Network Card firmware version 2.0.5: how to upgrade
3:44
Please watch this video to learn how to upgrade your Eaton Gigabit Network Card (Network-M2) to its latest firmware version 2.0. For more information: https://www.eaton.com/us/en-us/catalog/backup-power-ups-surge-it-power-distribution/eaton-gigabit-n
-
Eaton Gigabit Network-M3 card – Enhanced capabilities, unmatched security
0:15
Eaton Gigabit Network-M3 card – Enhanced capabilities, unmatched security